Report
How a Phone Number Can Reveal Your Entire Identity (Real OSINT Cases)
Two real OSINT cases showing how small exposed data points can turn into full identity pivots.
Report
Two real OSINT cases showing how small exposed data points can turn into full identity pivots.
Two real OSINT cases. Two different entry points. The same uncomfortable conclusion.
I was chatting with someone. Nothing unusual. At some point, I opened GetContact, not to investigate, just out of curiosity to see what tags other people had saved for their number.
GetContact is a free caller ID app. The way it works is simple: when someone saves your number in their phone under any name, that name gets crowdsourced into the app’s database. Search for a number, and you see every label anyone in the world has saved it under. Useful for identifying spam callers. Not what most people think about when they hand out their number.
What came back for this number was not just a name.
One tag included the name of a specific residential building. Another tag referenced a nickname that contained a location identifier. Scrolling further down, the city appeared as well.
Three crowdsourced tags. One building name. One city. Zero effort.
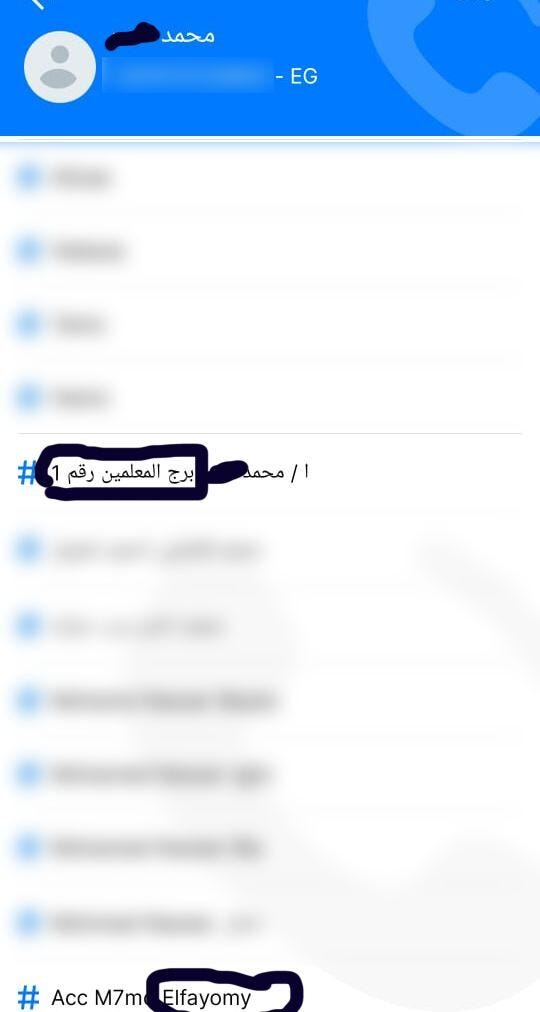
At this point, I had not done anything beyond searching for a phone number in a free app. I had not touched a terminal, run a script, or accessed anything private. And I already knew where this person lived.
The subject had left their GetContact username visible on their profile. That was the mistake that opened everything else.
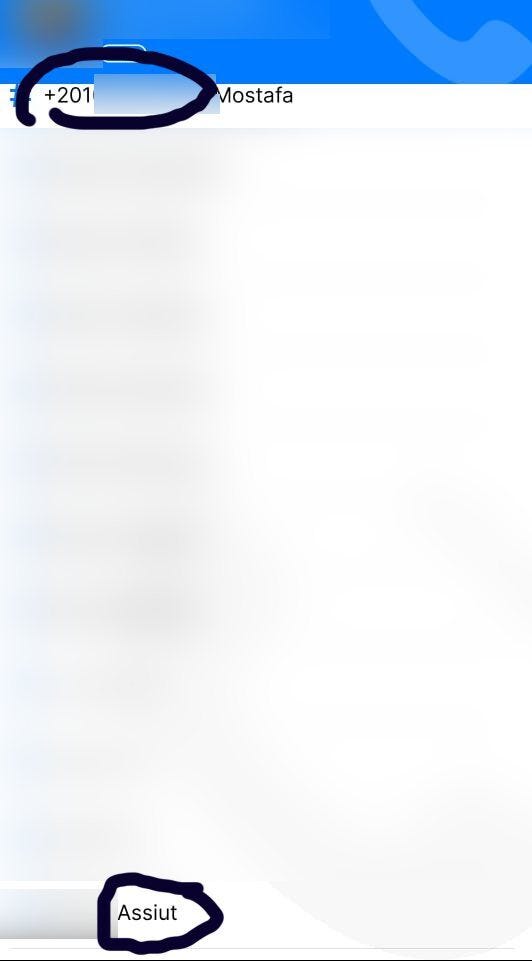
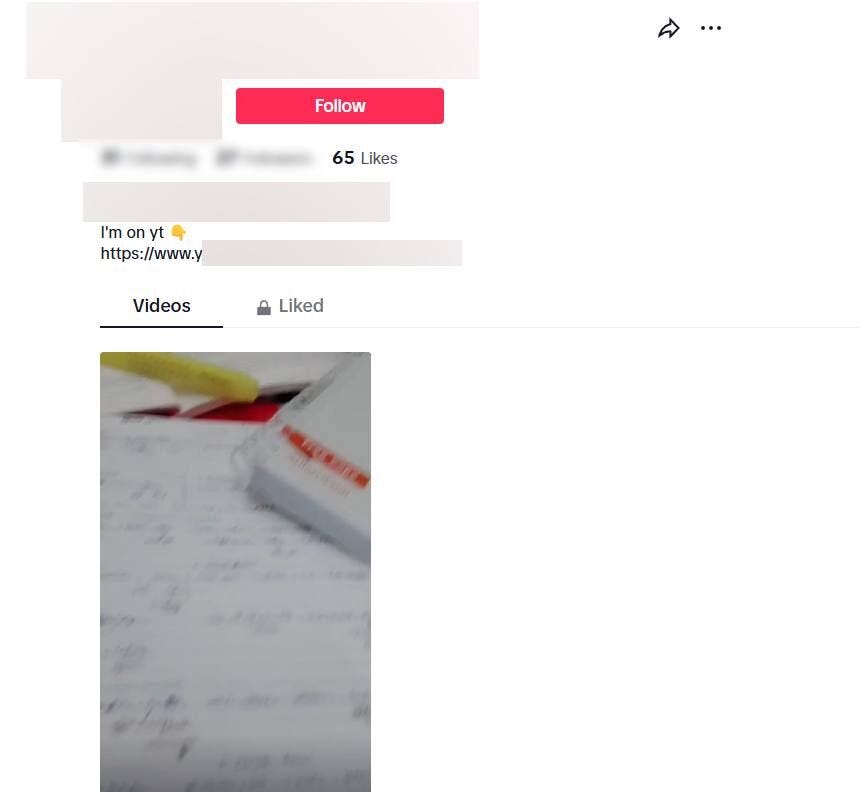
A username is a fingerprint. People create a handle once and reuse it across every platform they sign up for, including ones they forgot about years ago. I took the username and started searching.
TikTok came up almost immediately. A public profile, posted videos, and a YouTube channel link are sitting in the bio. The account had not been active recently, but it was fully public and indexed.
From the username pattern and what I could see on the TikTok profile, I was able to reconstruct the Gmail address tied to this person’s Google account. I ran it through GHunt, an open-source OSINT tool for Google account enumeration.
The output came back with:
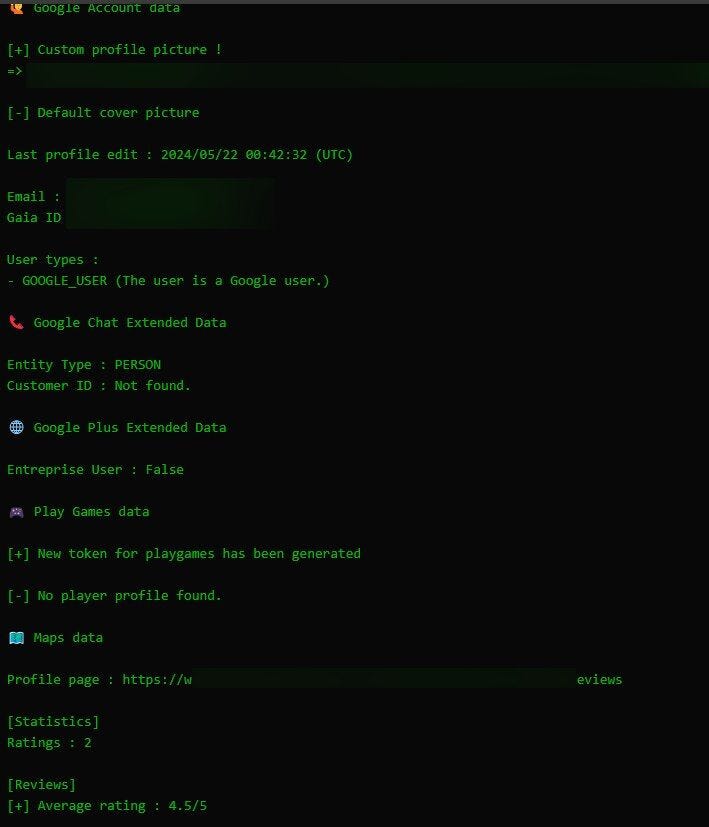
A phone number tag led to a username. A username led to a Gmail. A Gmail led to a confirmed Google identity with a real-world activity trail attached.
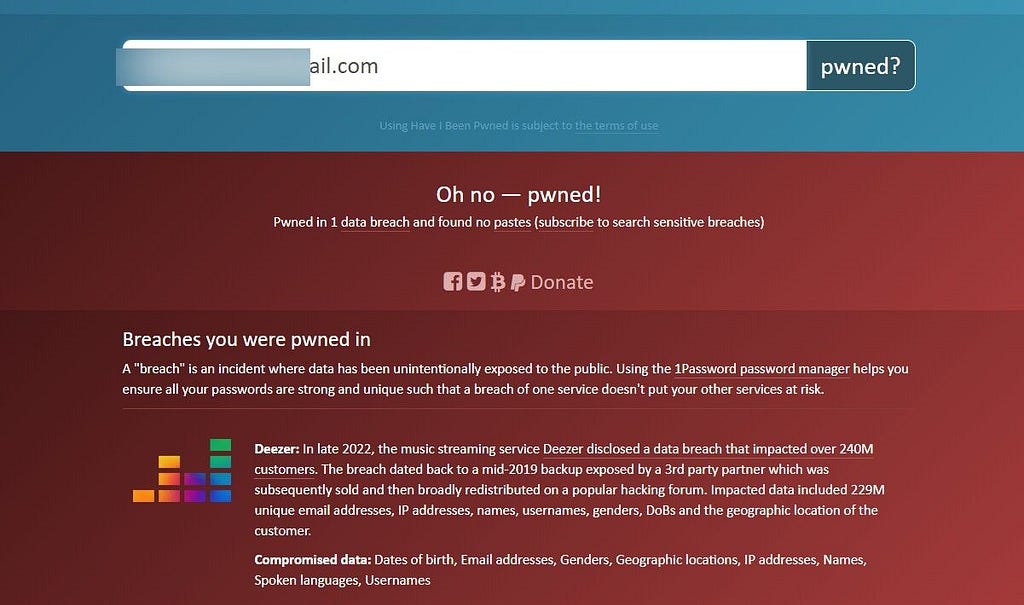
I ran the Gmail address through Have I Been Pwned.
One breach returned: Deezer. In late 2022, it was disclosed that a backup from 2019 had been leaked by a third-party partner and widely redistributed on hacking forums. The incident affected over 240 million accounts.
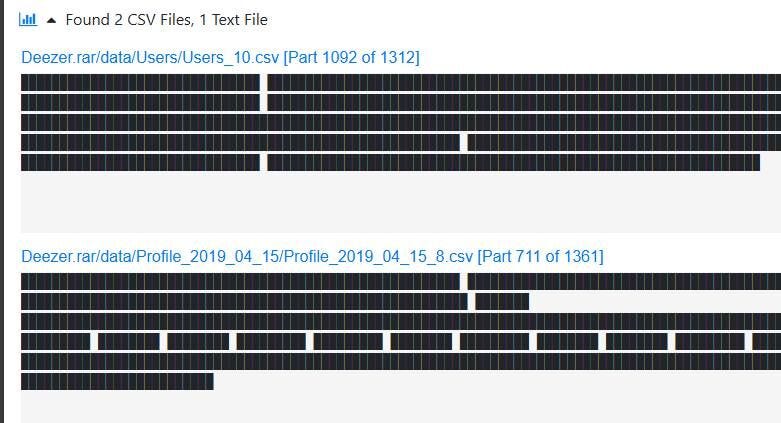
I pulled the raw breach files and searched for the email address. The record was sitting inside a CSV file, part 1092 of a 1312-part archive.
I also queried a Telegram bot that pulls structured records directly from breach dumps. I fed it the same email, and it returned the Deezer record cleanly formatted: full name, nickname, surname, date of birth, gender, country, registration date, and language.
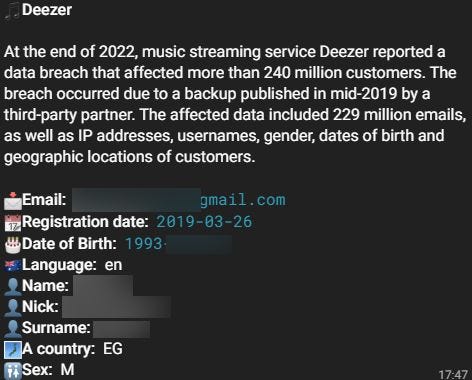
One breach. One email. A full identity record retrieved in seconds from a bot that anyone can access on Telegram.
Starting from a single phone number and a visible username, the investigation produced:
This is what a threat actor can do with that information: craft a phishing email that uses the correct name, references a real service the target used, and addresses them by their actual city and building. The data is not abstract. It is operational.
This is a separate incident. Different person, different entry point, same outcome.
I noticed someone had posted their CV directly in the comments section of a LinkedIn job post. Not an application through an official form. Not a message to a recruiter. A PDF, dropped publicly in a comment thread, visible to anyone who opened the post.
The person held a managerial role in cyber defense at a well-known international company.
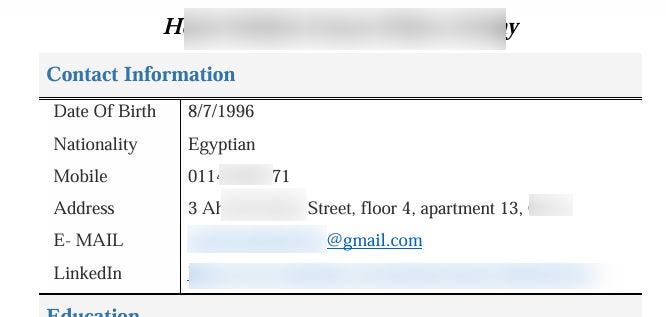
The CV contained the full name, date of birth, nationality, phone number, complete street address including floor and apartment number, personal Gmail address, and LinkedIn profile.
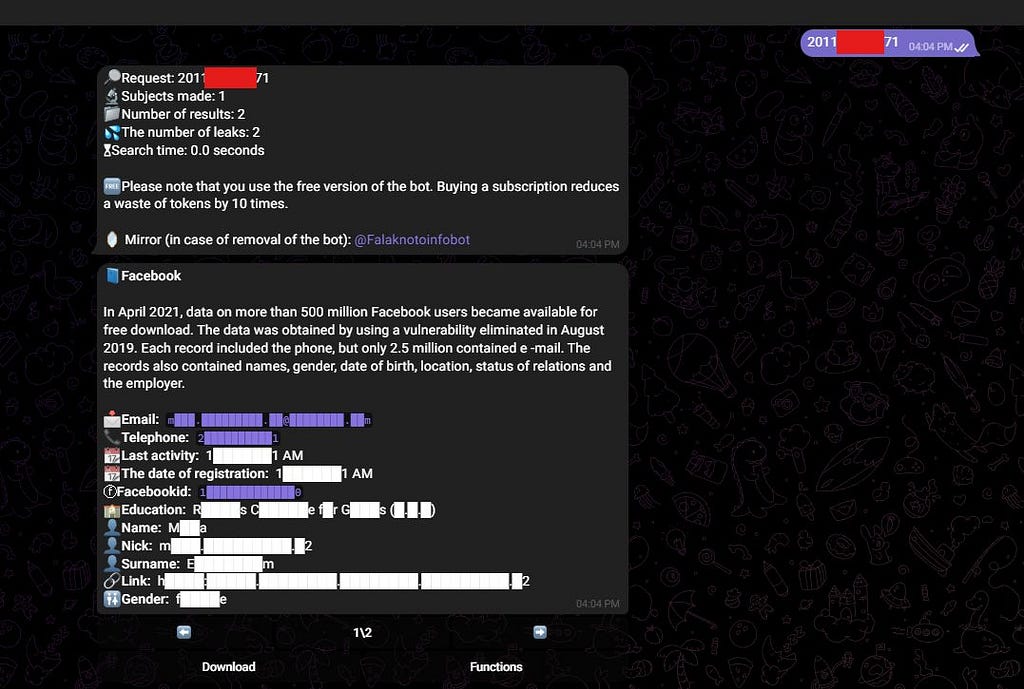
I ran the phone number through breach databases. The number returned a hit inside the Facebook 2021 dataset, where data on over 500 million users had been scraped via a vulnerability patched in 2019. The record added a second email address, a Facebook ID, registration and last activity dates, the university and faculty attended, full name, profile URL, and gender.
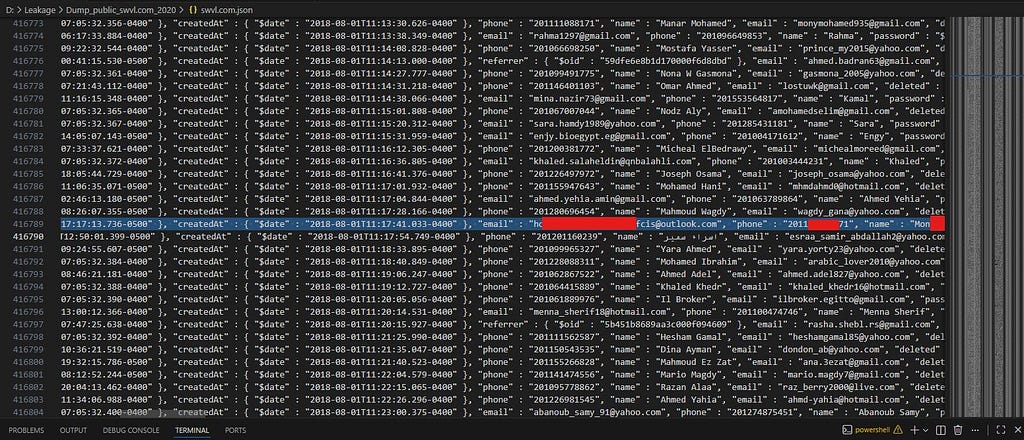
I then checked a local copy of the Swvl breach dump from 2020. Swvl is an Egyptian ride-hailing platform. Searching by the same phone number returned line 416789: the same number, the same name, a third email address, and an account creation timestamp from 2018.
Two breach records from a single phone number on a publicly posted CV. Combined with the full home address already visible on the document, an attacker now has everything needed for targeted phishing, impersonation, or physical profiling.
This person worked in cybersecurity. The failure was not ignorance of OSINT as a concept. The failure was not connecting that concept to their own personal behavior in a public space.
Neither subject did anything that felt like a serious mistake in the moment. One left a username visible on a caller ID app. One dropped a CV in a job post comment. Both actions are normal, ordinary, and something millions of people do every day.
The problem is not any single action. The problem is that each piece of data you leave in a public space is a node, and every node connects to other nodes through breach databases, OSINT tools, social platforms, and records that have been freely circulating for years.
The tools used across both investigations:
No exploits. No special access. No illegal activity. Just public tools and data that should never have been left exposed in the first place.
1. Clean your GetContact tags. Go to the GetContact account management page, search for your number, and delete any tags that reveal sensitive information. Building names, addresses, family members’ names, and secondary numbers. Remove them.
2. Check your breach exposure. Run your email addresses through Have I Been Pwned. If you appear in a breach, that record is already out there. Knowing it exists changes how you think about every account and password connected to it.
3. Stop posting your CV publicly. Apply through official career pages, verified recruiter emails, or LinkedIn’s built-in application system. A PDF in a public comment section is a public data dump. It will be indexed, downloaded, and searched by people you do not know.
4. Treat your phone number as a sensitive credential. Your number is often the primary key that links your identity across dozens of services and breach records. Be deliberate about where you share it.
5. Search yourself regularly. Google your phone number. Google your email addresses. Search your username across platforms. You cannot protect what you do not know is exposed.
The gap between “I just shared my number” and “someone now has a complete operational profile on me” is smaller than most people want to believe.
Both of these cases happened. The data was sitting there, public, indexed, and waiting. Neither subject knew someone had looked.
Take five minutes today. Clean your tags. Check your breaches. Stop handing people the master key.